![PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/df932f9db948e0e49c26a748ca2eec9d76e3c118/5-Figure3-1.png)
PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar

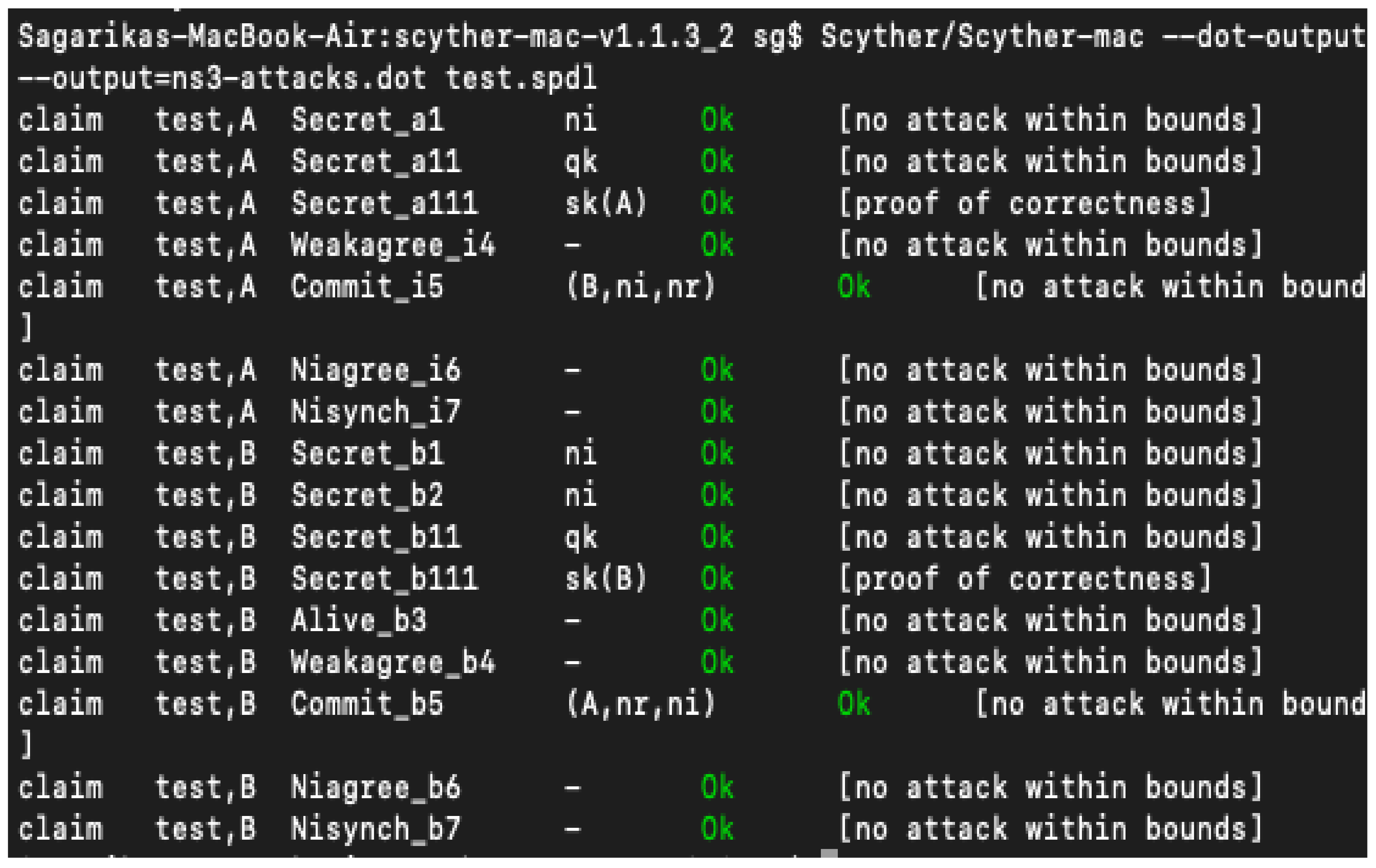
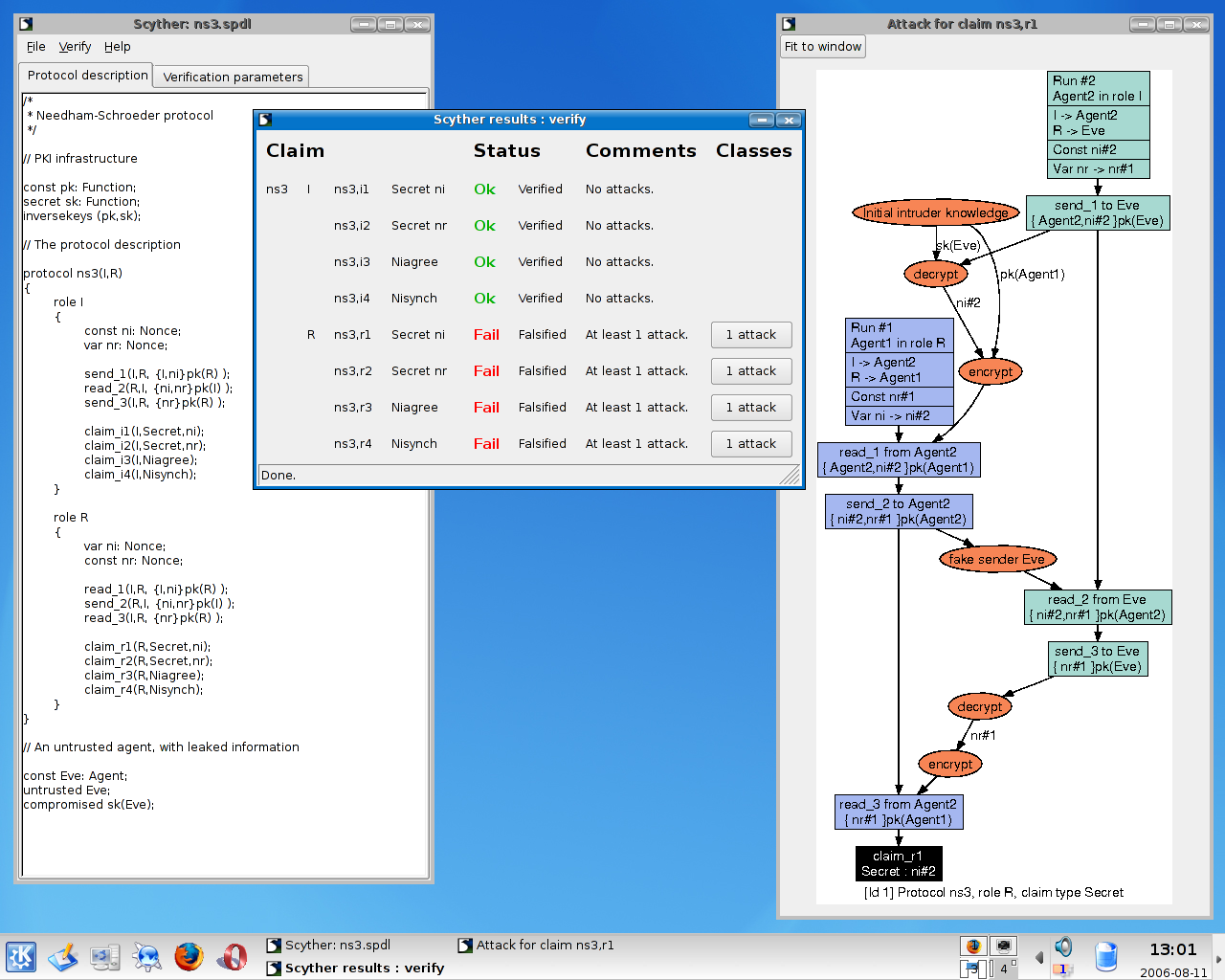
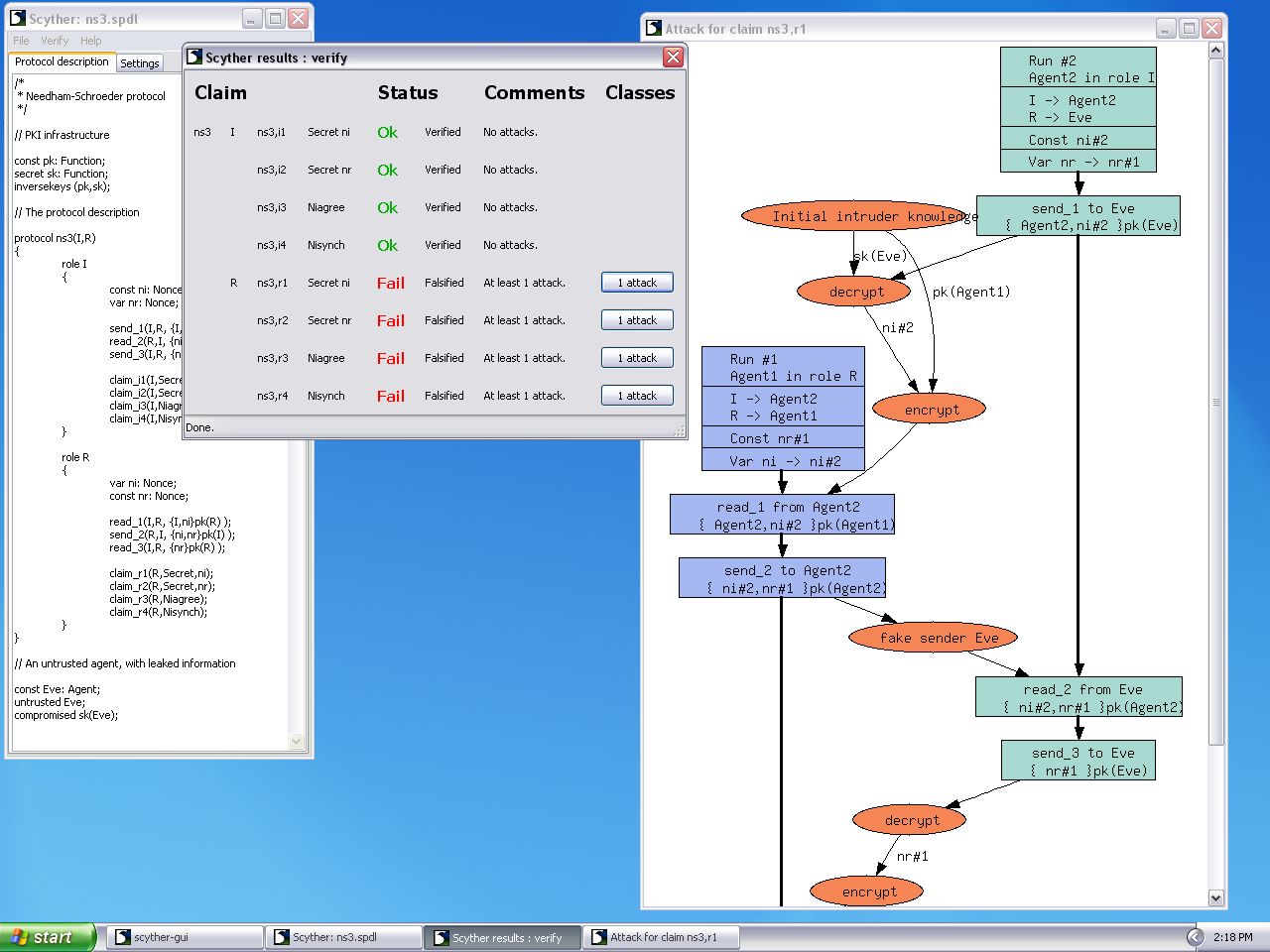
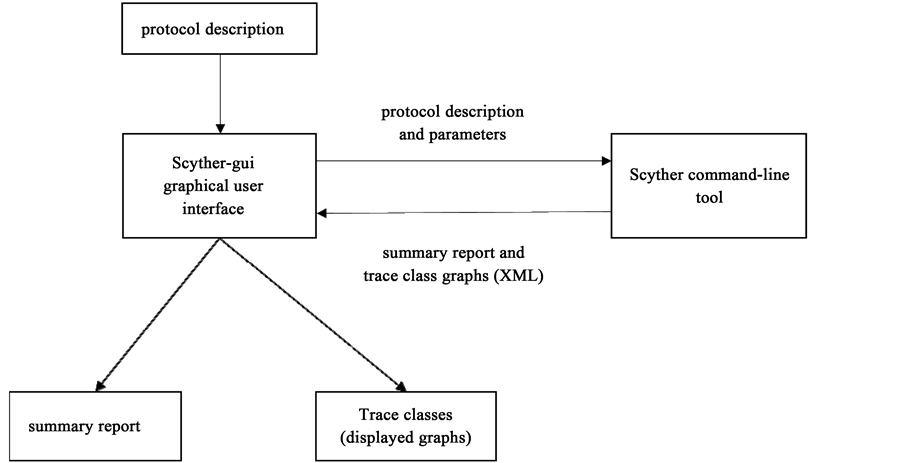
The results using 'verification claim' procedure in Scyther tool (see... | Download Scientific Diagram

Result using 'automatic claim' procedure in Scyther tool (see online... | Download Scientific Diagram
Applied Sciences | Free Full-Text | An Intrusion Resistant SCADA Framework Based on Quantum and Post-Quantum Scheme | HTML
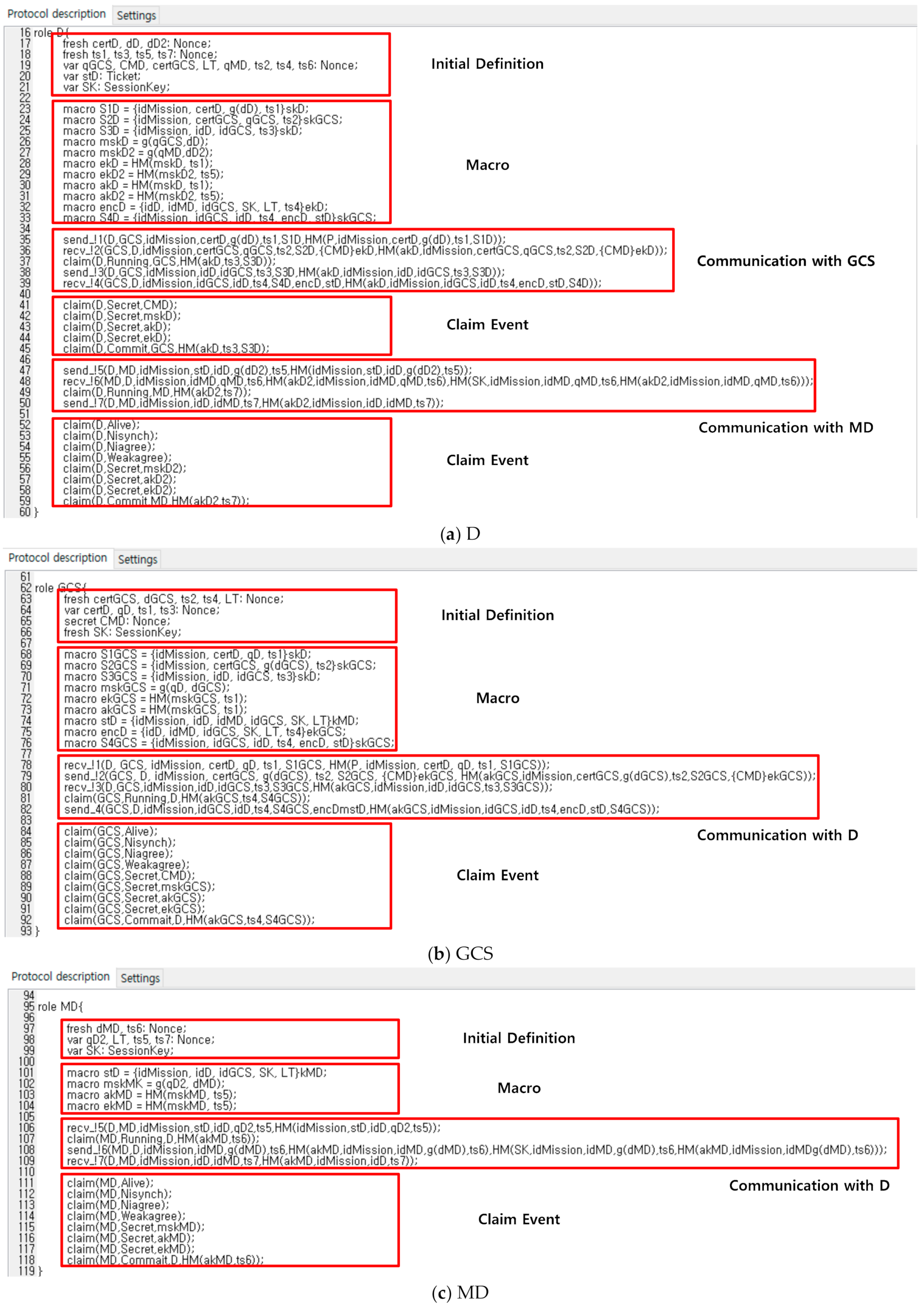
Sensors | Free Full-Text | Drone Secure Communication Protocol for Future Sensitive Applications in Military Zone | HTML

The results using 'verification claim' procedure in Scyther tool (see... | Download Scientific Diagram
![PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/df932f9db948e0e49c26a748ca2eec9d76e3c118/6-Figure4-1.png)
PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar

The results using 'verification claim' procedure in Scyther tool (see... | Download Scientific Diagram

On the designing a secure biometric-based remote patient authentication scheme for mobile healthcare environments | SpringerLink

An online security protocol for NFC payment: Formally analyzed by the scyther tool | Semantic Scholar






![PDF] Verifying Group Authentication Protocols by Scyther | Semantic Scholar PDF] Verifying Group Authentication Protocols by Scyther | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/afecefc52bb5c36f7b968eac7aaf7c24361b5813/12-Figure3-1.png)



