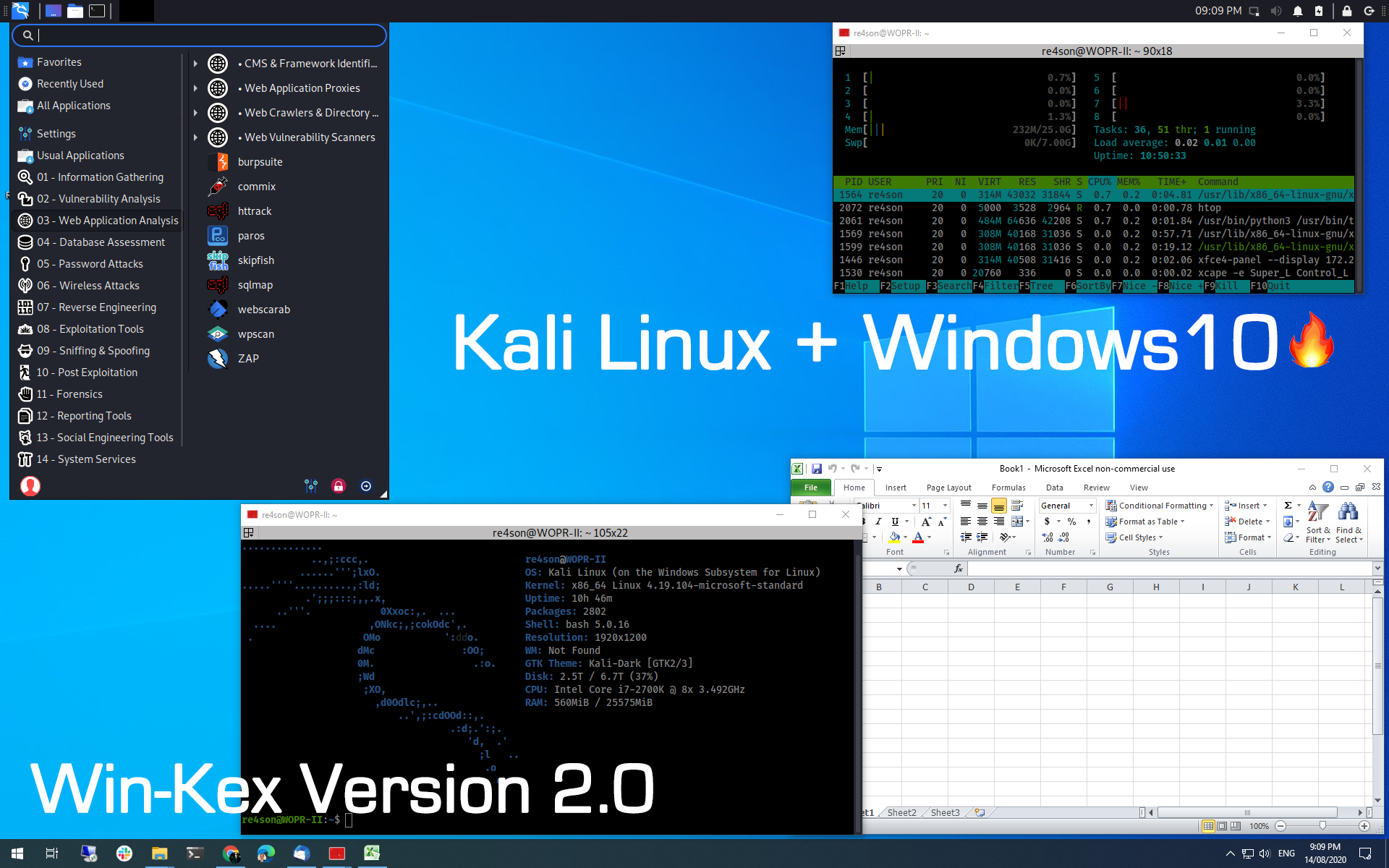
Pentesting on Windows. Kali 2020.3 is here! In this article we… | by 👨💻Siddharth | InfoSec Write-ups
Pentest Tools Framework - A Database Of Exploits, Scanners And Tools For Penetration Testing - Hacking Land - Hack, Crack and Pentest

Pentest-Tools-Auto-Installer - A Simple Tool For Installing Pentest Tools And Forensic Tools On Debian / Ubuntu Based OS – PentestTools
PentestBox - excellent penetration testing environment on Windows - SEO Consultants, Digital Marketing, WordPress Development
GitHub - R3dy/capsulecorp-pentest: Vagrant VirtualBox environment for conducting an internal network penetration test
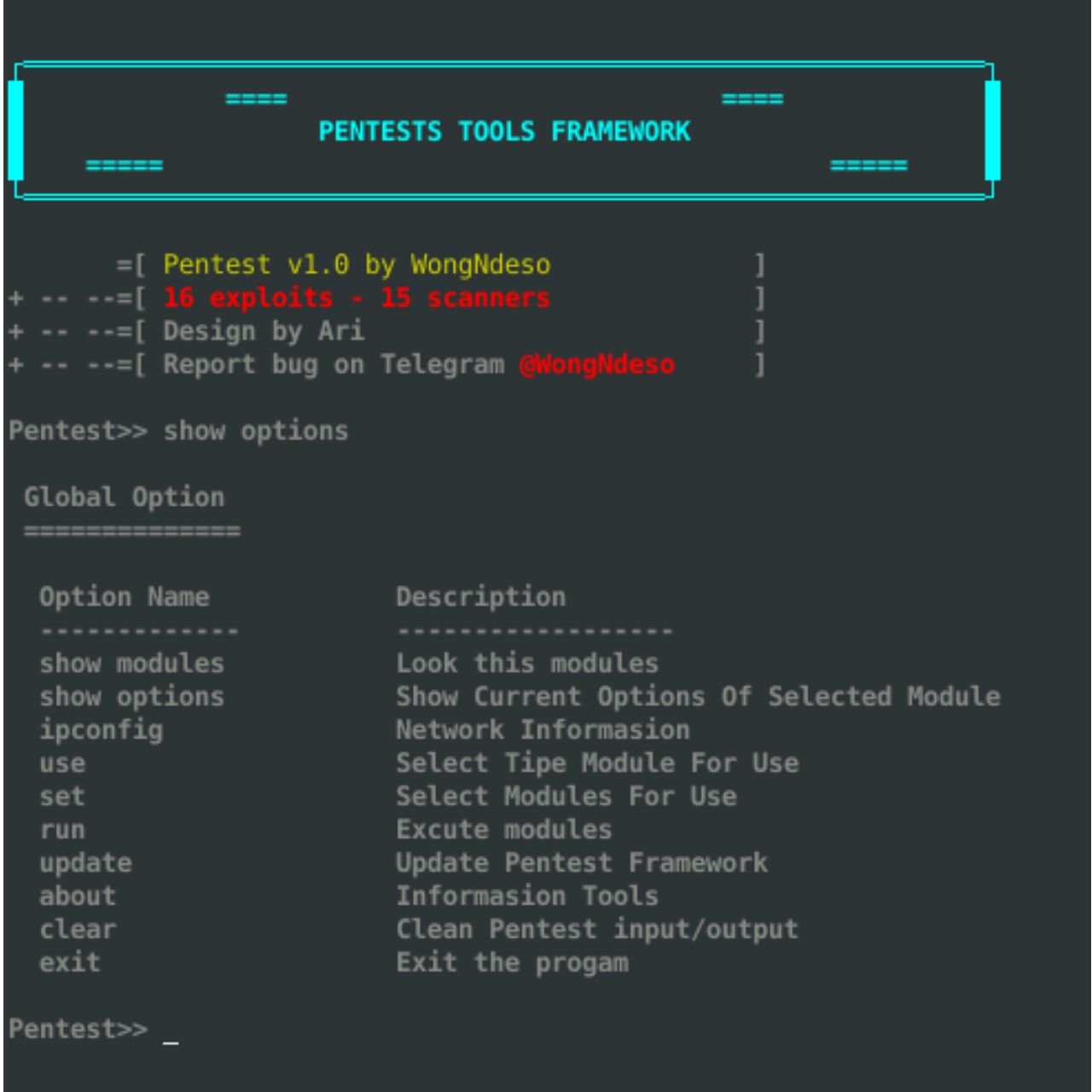
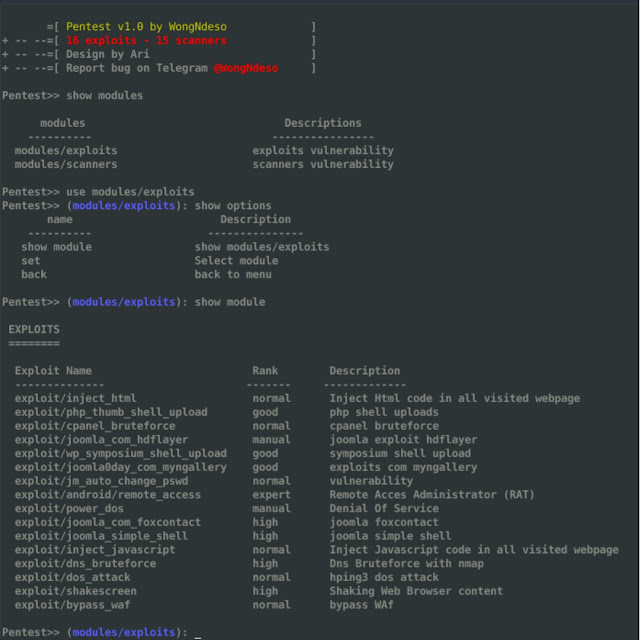
GitHub - 3xploit-db/Pentest-Tools-Framework: Pentest Tools Framework is a database of exploits, Scanners and tools for penetration testing. Pentest is a powerful framework includes a lot of tools for beginners. You can explore





![New scanners] Detect SMBGhost and Ghostcat vulnerabilities with Pentest- Tools.com New scanners] Detect SMBGhost and Ghostcat vulnerabilities with Pentest- Tools.com](https://pentest-tools.com/blog/wp-content/uploads/2020/05/smbghost-vulnerability-scanner-report.png)

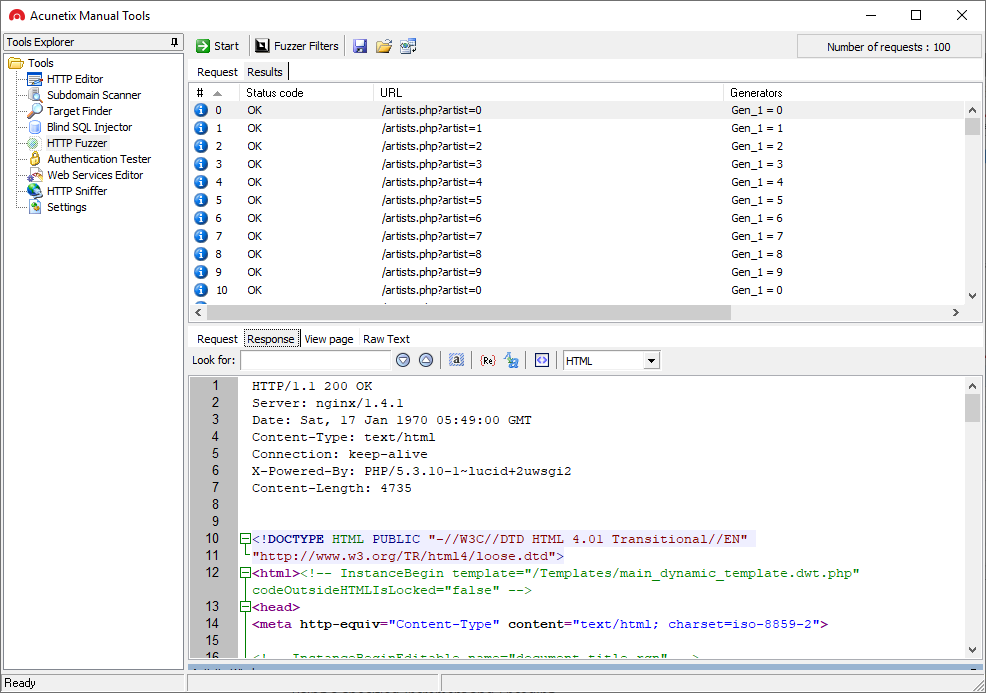
![95 Top Penetration Testing Tools That Actually Work [Updated 2019] 95 Top Penetration Testing Tools That Actually Work [Updated 2019]](https://cyberx.tech/wp-content/uploads/Ophcrack-Hacking-Tool-585x439.jpg)